Security testing for SaaS is no longer a negotiable issue among SaaS CTOs. As the number of smartphone users throughout the planet reaches 6.92 billion and the apps market is almost saturated with approximately five million apps, the attack surface has increased manifold.
SaaS applications are used in a multi-tenant and distributed nature, which presents distinct vulnerabilities. These vulnerabilities are used by the attacker as API attacks, poorly configured cloud storage, and insecure third-party integrations.
A recent survey indicated that 89% of enterprises currently demand SaaS providers to produce compliance certifications to be able to sign contracts. Security testing for SaaS products has become more of a business differentiator than a technical issue. Security testing services confirm encryption protocols, access controls, and practices of data handling throughout the application lifecycle.
Why Security Testing is Critical for SaaS Products
➔ Protecting Customer Data and Privacy
SaaS systems store enormous volumes of confidential data, which are subject to attack by hackers. Multi-layer protection is necessary in terms of customer records, financial data, and authentication credentials. One act of vulnerability has the potential to reveal the user accounts of millions of users, as shown in the high-profile breaches of companies such as SolarWinds and Facebook.
Security testing service providers assist in pointing out the weak points before they are exploited by attackers. Periodic testing reveals access control vulnerabilities, encryption loopholes, and data leakage vulnerabilities that would otherwise remain invisible.
➔ Ensuring Compliance with Industry Regulations
Scaling software firms often require diverse regulatory certifications like SOC 2 and ISO 27001 compliance. These frameworks require certain security controls, audit trails, and data protection.
To escape lawsuits and fines, there must be records of security care. Failure to comply may attract fines of millions of dollars, especially with the strict enforcement regime of GDPR.
Compliance audits look into the alignment of software security testing services with the requirements of the regulations. Organizations should be capable of constant monitoring, vulnerability management, and incident response.
➔ Maintaining Trust and Brand Reputation
Studies indicate that three out of four customers will not utilize a SaaS product that does not have clear security credentials.
Trust is a major distinguishing factor of SaaS platforms in saturated markets. In situations where competitors have comparable features and prices, purchasing decisions are frequently influenced by the state of security posture.
Reputational damage spreads rapidly using social media and increases the magnitude of any security incident. One violation can create a wave of distrust since consumers are quick to post negative experiences on the internet.
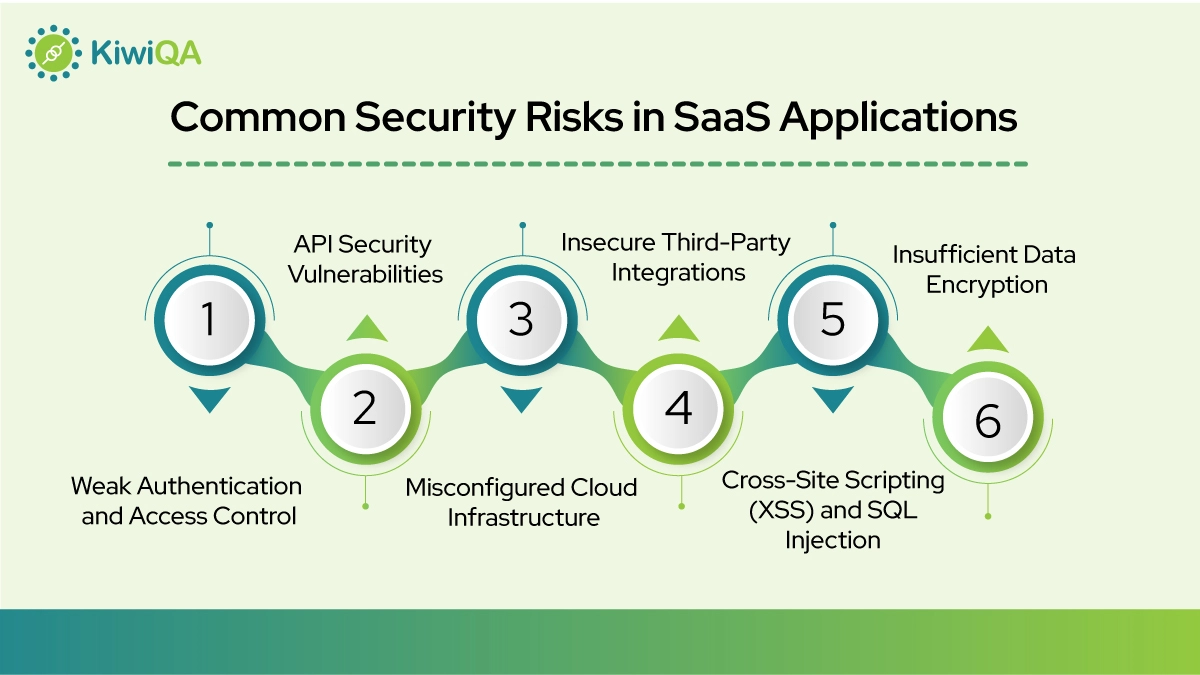
Common Security Risks in SaaS Applications
➢ Weak authentication and access control: Account takeover attacks are easy, as many platforms continue to use simple passwords and do not have multi-factor authentication.
➢ API vulnerabilities: Unprotected endpoints, a lack of rate limiting, and broken authentication enable unauthorized access and manipulation of data.
➢ Misconfigured cloud infrastructure: Sensitive information is often disclosed by open storage buckets, overly generous permissions, and a deactivated security setting.
➢ Unsecure third-party integrations present foreign attack vectors. SaaS platforms that lack the integration of poorly secured APIs or SDKs inherit these vulnerabilities.
➢ Cross-site scripting (XSS) and SQL injection: These attacks are used to exploit application logic in order to compromise data or to execute an injected malicious code.
➢ Insufficient encryption of sensitive data: Data should be encrypted during transit and at rest with high-level cryptographic algorithms.
Also Read : Top Security Testing Company in UK for Compliance and Data Protection
A CTO’s Security Testing Checklist for SaaS Products
➨ Application Security Testing
Static Application Security Testing (SAST) is conducted on source code and does not involve the execution of the application. This method detects weaknesses in coding, unsafe design, and any possible vulnerabilities during the early stages of development.
Dynamic Application Security Testing (DAST) looks at running applications in an external analysis. It emulates the actions of an attacker in a bid to find runtime vulnerabilities that would be overlooked by the static analysis.
Secure code reviews and vulnerability scanning combine automated tools with human expertise. Security testing service teams conduct a manual inspection of the critical code paths, and automated scanners are used to detect the existing vulnerability patterns.
➨ API Security Testing
Authentication and authorization mechanisms must be validated to make sure that only legitimate users use protected resources. Test every endpoint for proper credential verification and permission enforcement.
API testing prevents attackers from altering database requests or terminal instructions. The API security can be compromised by SQL injection, shell penetrations, and directory service probes.
Resource exhaustion attacks are controlled by monitoring, rate limiting, and API abuse protection. Without proper throttling, attackers can overwhelm systems or scrape sensitive data.
➨ Cloud Infrastructure Security Testing
Checking cloud settings and authorization identifies errors that tend to leak data. Review IAM policies, security groups, and network configurations against best practices.
Finding open ports, misconfigured storage, and exposed services can prevent unauthorized access. These problems are identified by automated scanning tools, although they can be validated through manual inspection.
This constant surveillance of cloud resources means that security does not diminish with time. Change drift and unwarranted alterations should raise warning bells.
➨ Authentication and Access Control Testing
Multi-factor authentication testing ensures that other authentication factors enhance security. Implementation of Test MFA to overcome bypass vulnerabilities and user experience problems.
Role-based access control authentication ensures that users are only allowed to access resources in line with their roles. Provide tests on paths of privilege elevation and horizontal access control.
Session management test is a way of making sure that the sessions have the right expiry time and they cannot be hijacked. Confirm that there are mechanisms that generate, store, and invalidate session tokens.
➨ Data Protection Testing
Encryption testing for data at rest and in transit is carried out to ensure that sensitive data is secured. Check good cipher suites, key management, and full encryption.
Secure storage validation checks that credentials, tokens, and sensitive data are not stored in plaintext. Examine database encryption, file system, and memory.
Data masking and tokenization checks make sure that only sensitive data is displayed when it is necessary. Ensure logging, error messages, and analytics do not reveal any hidden information.
➨ Penetration Testing
A simulated real-world cyber attack exposes the reaction of systems to perseverant attackers. Penetration testers use automated tools with manual tools to detect complex vulnerabilities.
Detecting vulnerabilities earlier than attackers gives important time to fix them. Security testing solutions provided on the basis of penetration testing provide a realistic risk evaluation.
Testing the efficacy of remediation verifies that fixes in fact fix known problems. Post-remediation testing is to verify that the vulnerabilities do not exist and are not recurrent.
Security Testing Tools Commonly Used for SaaS Platforms
✧ OWASP ZAP is an open-source tool that detects typical security issues and provides elaborate reports.
✧ Burp Suite is the standard of web security testing. Its proxy, scanner, and manual testing tools allow in-depth application testing.
✧ Nessus identifies vulnerabilities in infrastructure in networks and systems. It detects gaps in patches, configuration errors, and rules violations.
✧ Snyk specializes in open-source dependency security. It identifies vulnerable libraries in code repositories and container images and proposes remedies.
✧ Metasploit can also be used to perform advanced penetration testing by simulating exploits. It is used by security teams to authenticate the existence of vulnerabilities that have been identified as exploitable.
Best Practices for Implementing SaaS Security Testing
✧ Security testing that is integrated into the CI/CD pipelines will make sure that vulnerabilities are identified early. Security scanners must be automated to execute each code commit and deployment.
✧ Conducting frequent vulnerability testing keeps the system secure as the applications get modified. Arrange regular evaluations every quarter at the least, and have more frequent evaluations of vital elements.
✧ Threat detection and continuous monitoring ensure that the emerging threats are addressed as soon as possible. Security testing services company partners can provide 24/7 monitoring capabilities.
✧ Implementing DevSecOps practices weaves safety across the entire engineering timeline. Security is made the responsibility of all and not an afterthought.
✧ Vulnerabilities are avoided by training development teams on secure coding standards. Training updates allow the teams to stay abreast of new threats.
How Automated Security Testing Improves SaaS Protection
Faster vulnerability detection leads to a quicker remediation process because the issues are identified as quickly as possible. Automated scans take minutes, as opposed to the days needed to conduct manual testing.
Continuous security validation during development helps to prevent the release of vulnerabilities into production. Programmers get real-time feedback on the effect of their program on security.
Reduced manual testing effort enables the security personnel to work on difficult scenarios that involve human judgment. Repetitive checks are done using automation, and more complex threats are solved by experts.
Early risk identification before deployment reduces the costs of remediation exponentially. The cost of correcting security problems in development is much lower than fixing production systems.
Security testing solutions provide expansion capabilities that remain unattainable via human-led assessments. With the increase in complexity of applications, automation is necessary.
Also Read : 5 Advanced Penetration Testing Techniques Every QA Professional Should Know
When CTOs Should Partner with Security Testing Experts
The cost of scaling SaaS systems using complex infrastructure is sometimes out of reach of internal security teams.
The added value of conducting compliance audits is to have expert knowledge of the regulatory requirements. Security testing company specialists are aware of what the auditors require and how to prove their compliance accordingly.
Advanced penetration testing takes skills that are not necessarily retained by many organizations.
Building long-term security testing strategies takes skills that are not necessarily retained by many organizations. Specialists collaborate to develop road scales to match business expansion and threat developments.
Ready to Secure Your SaaS Platform? Get a Security Testing Consultation Today
SaaS is a type of service that requires security testing to prevent changes in cyber threats. The cost of SaaS application security testing pays dividends through preventing breaches, maintaining compliance, and customer confidence.
Security gaps have no structured validation until they are exploited by attackers. Team up with an established security testing services company and make your SaaS security posture much more secure.
Security testing for SaaS products requires ongoing commitment rather than a one-time effort. Threats evolve, applications change, and new vulnerabilities emerge constantly.










Comments are closed.